Security
Experience the power of security. Protect individuals and organizations with advanced technology and cybersecurity measures for a safer world.
The Blockchain and The Byzantine Generals Problem
Twenty years ago, nobody would have predicted the impact that a popularized global information network would have on society–and even though the internet has only been around for a little over two decades, we still have yet to max out its potential, with wearables, connected home devices, and other Internet of Things (IoT) components just recently becoming popular. Nevertheless our dependence on the worldwide web is easily demonstrated. For example, in 2014, it was calculated that $1.2 million dollars worth of business was done every 30 seconds online, and Pew Research released a report showing that only about 13 percent of Americans don’t use the internet. You would think that…
4 Things a Business Needs to Understand About Data Breaches
Data breaches have become a fact of life for businesses. Ruthless hackers infiltrate systems, injecting malware and stealing vital information from companies. You must protect your organization from them. When you can’t, you must behave proactively to lessen the damage. Here are four things a business needs to understand about data breaches.
The Benefits of Mobile Device Management
Today businesses and companies develop and evolve faster than you read this article. They expand and so require more and more technical support to ensure that work it done properly and in time. For this reason more and more businesses today use mobile device management systems or at least consider doing so. Mobile device management systems were created and developed to simplify usage of several mobile devices at a time, regulate file transferring between them, improve cooperation between workers and departments, and many other reasons. But the main point of their existence is to let users of different devices synchronize them and use same set of files and documents from…
Is Your Construction Site Security Lax? Here’s How To Improve It!
Because construction sites are such busy places, it can sometimes be hard to keep on top of security. As a result, some thieves take advantage of that fact. They could steal plant machinery and power tools in broad daylight if they wished! Of course, it doesn't have to be that way. There are some practical steps that you can take.
Did you Backup your Computer Today?
When was the last time you backed up your computer? Last week? Last year? Never? A good backup plan can save your tail, but for some, this realization comes too little too late, and they're left scrambling to recover crucial files. Consider this: only 50% of all enterprises back up their computers to some form of endpoint backup.
Understanding MPLS and its Benefits to Businesses
Multi-Protocol Label Switching (MPLS) is the latest communications technology that uses packet labels thru routing protocols to send and receive data across the web and other paths that exist for telecom carriers.
5 Practical Ways to Check If a Website Is Legitimate
While we often feel safe browsing online from the comfort of our home or office, the worldwide web is not necessarily always a nice safe place. There are plenty of wonderful websites and companies online that provide us with quality service and ensure that they will keep our information safe. Unfortunately, not every site works this way.
Simple and Easy Ways to Keep Your Smartphone and Data Protected
Keeping your phone safe is imperative. While we have come to depend on smart technology, it’s important to remember that our phones contain a raft of personal information. If this data or information were to get into the wrong hands, it could have a severe impact on our reputation. But, worse, it could leave us susceptible to information theft and fraud. Now, our phones don’t just contain information from emails. We use our phones for banking and other financial transactions. When it comes to keeping your smartphone safe, there are some easy and simple ways that you can do this. Lock Screen Security Even leaving your phone unattended for a…
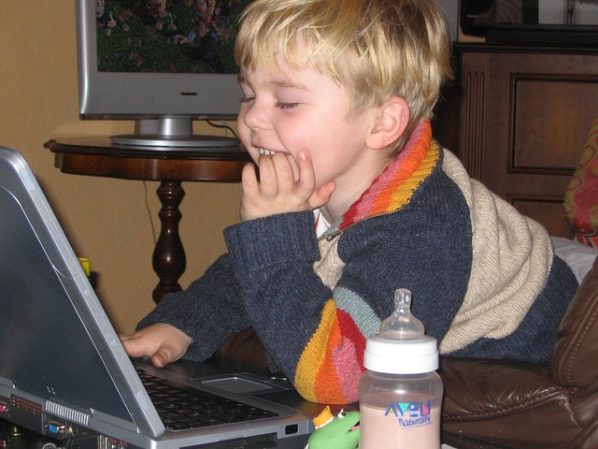
How to Keep Your Children Safe on the Internet?
You can always help your child with the internet usage and also guide him/her about the internet scams to make them aware about the misuse of internet. There is a lot more you can do to save them from internet crimes. Have a look.
How to Safely Store Your Data in the Cloud
Using the Internet for business purposes is becoming one of the main reasons in general for using the global network. Of course, this statement is negotiable if we know how many kids are on social networks 24/7, but a certain hedge can be comprised in the claim that most employed adults today come to the Internet in order to improve their business results. To go further, it is not too bold to say that even those workers who don’t use the Internet as a business mediator or the means of handling their business(es), but just for fun, have their business results also dependent on the time they spend on the…
Armenian Government Ministries Websites Suffered from Cyber Attack
A group of Azerbaijan hackers from Azerbaijan Hacker Team has hacked a number of Armenian Government ministers' websites, and placed a video on their defaced page. There are a total of 64 websites hacked including Ministry of Education, police, city districts, Artsakh State University, Football Federation of Armenia and several other Armenian websites.
German Users’ Data Compromised Due to Botnet Malware Attack
16 million German users suffered from a Botnet malware attack whose digital identities had been stolen. The data was linked with Facebook accounts, mail accounts, Amazon accounts, and other online services. The attack was revealed when Germany's Federal Office for Information Security (BSI) ran a Botnet analysis.